March 21, 2026
Enterprise
Marketplace
Multi-Vendor
Multi-vendor marketplaces present unique security challenges that traditional ecommerce platforms don’t face. With multiple vendors accessing sensitive customer data, payment information, and inventory systems, enterprise organisations must implement robust security controls from day one. This comprehensive guide walks you through the critical preparation, execution, and verification steps needed to build a secure multi-vendor marketplace that protects your business, vendors, and customers whilst maintaining operational efficiency and regulatory compliance.
Table of Contents
Key takeaways
Assessing requirements and preparing your marketplace environment
Step-by-step execution of secure marketplace setup
Verification, continuous compliance and vulnerability management
Secure your enterprise multi-vendor marketplace with Ultra Commerce
Frequently asked questions about secure marketplace setup
Key Takeaways
Point | Details |
|---|---|
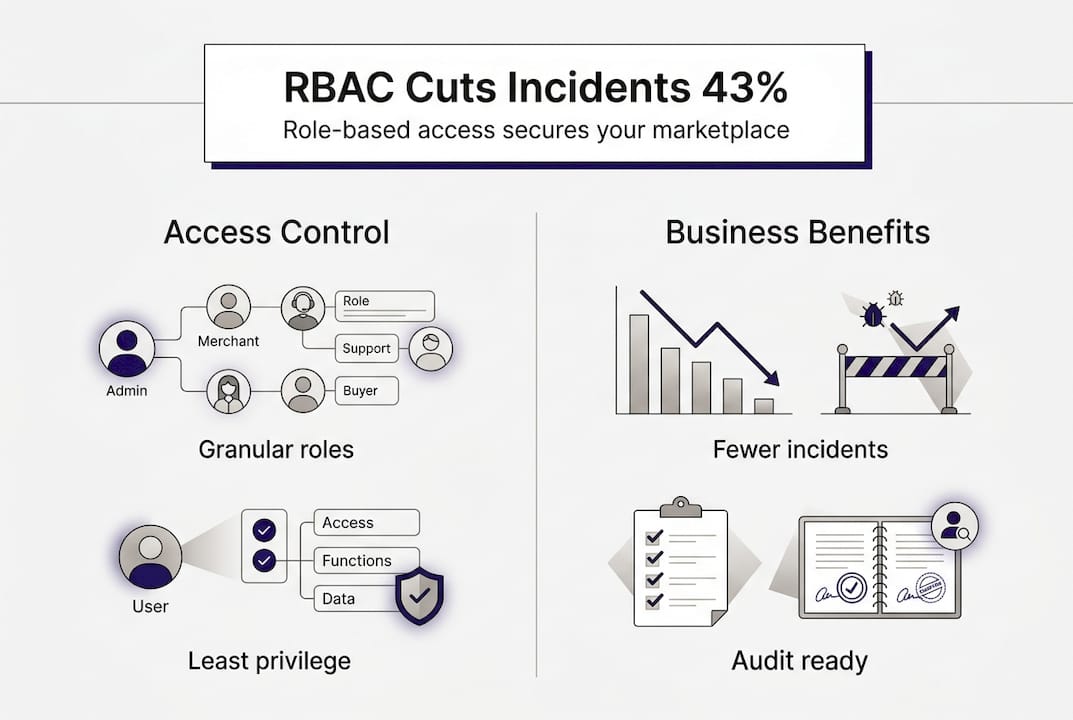
RBAC reduces incidents | Role based access control reduces security incidents by 43 per cent by granting granular permissions so vendors access only their own data. |
OAuth 2 reduces risk | OAuth 2 protocols reduce security incidents by 43 per cent compared with basic authentication methods. |
Compliance from outset | Compliance from outset shapes the architecture to meet PCI DSS and GDPR requirements and avoid technical debt. |
Microservices isolation | Modular microservices architecture contains breaches and allows independent scaling of critical functions. |
Continuous vulnerability management | Continuous vulnerability management is essential to keep the marketplace secure across vendors and systems. |
Assessing requirements and preparing your marketplace environment
Before launching your multi-vendor marketplace, you must establish a security-first foundation that addresses both immediate operational needs and long-term scalability. Enterprise marketplaces require more sophisticated access controls than single-vendor platforms because each vendor represents a potential security vulnerability.
Start by implementing role-based access control that grants granular permissions to each vendor. OAuth 2.0 protocols reduce security incidents by 43% compared to basic authentication methods. This approach ensures vendors can only access their own product catalogues, order data, and customer information without exposing other vendors’ data or your platform’s core systems.
Regulatory compliance must shape your architecture from the beginning. PCI-DSS requirements mandate secure payment processing with network segmentation and encrypted data transmission. GDPR compliance requires explicit consent mechanisms, data portability features, and the ability to delete customer information across all vendor systems. Building these capabilities after launch creates technical debt and potential legal exposure.
Modular microservices architecture provides the flexibility and security isolation enterprise marketplaces need. Rather than a monolithic system where one vulnerability compromises everything, microservices contain breaches and allow independent scaling of critical functions. Your vendor management, payment processing, and inventory systems should operate as separate services with defined API boundaries.
Create a comprehensive requirements checklist covering:
Hardware infrastructure with redundancy and failover capabilities
TLS 1.3 support across all systems and endpoints
Network segmentation separating vendor access from core systems
Certificate management policies with automated renewal
Audit logging infrastructure capturing all vendor actions
Backup and disaster recovery procedures tested quarterly
Pro Tip: Establish security requirements in vendor contracts before onboarding. Require vendors to maintain specific security certifications and agree to regular audits. This contractual foundation makes enforcement straightforward and protects your marketplace from vendor negligence.
Your vendor dashboard security deserves special attention because it’s the primary attack surface. Implement multi-factor authentication, session timeouts, and IP allowlisting for vendor accounts. Monitor login patterns to detect credential stuffing attacks and compromised accounts. These preventive measures are far more cost-effective than responding to breaches.
Internal audit capabilities should provide real-time visibility into vendor activities, system access patterns, and data flows. Security teams need dashboards showing active sessions, permission changes, and unusual behaviour patterns. Executive stakeholders require compliance scorecards demonstrating regulatory adherence and risk posture. Building these reporting tools during initial setup ensures you can demonstrate security to auditors, partners, and customers.
Requirement category | Essential components | Compliance impact |
|---|---|---|
Access control | OAuth 2.0, MFA, RBAC | PCI-DSS, GDPR |
Encryption | TLS 1.3, at-rest encryption | PCI-DSS |
Network security | Segmentation, WAF, DDoS protection | PCI-DSS |
Monitoring | SIEM, audit logs, alerting | GDPR, SOC 2 |
Step-by-step execution of secure marketplace setup
With requirements defined, execute your secure marketplace implementation following a structured approach that prioritises security at each layer. Begin with identity and access management as your foundation. Configure OAuth 2.0 authentication servers that issue time-limited tokens for vendor API access. Each vendor receives unique client credentials that map to specific permission sets defined in your RBAC system.
Granular permissions should follow the principle of least privilege. A vendor managing electronics shouldn’t access fashion category data. Vendors fulfilling orders don’t need access to pricing strategy tools. Create permission matrices mapping vendor roles to specific API endpoints and data resources. This isolation prevents lateral movement if credentials are compromised.
Implement end-to-end encryption for all data exchanges using TLS 1.3, which provides forward secrecy and eliminates known vulnerabilities in older protocols. Configure certificate pinning for mobile applications to prevent man-in-the-middle attacks. Encrypt sensitive data at rest using AES-256 encryption with proper key management through hardware security modules or cloud key management services.
Certificate management policies must include:
Automated certificate renewal 30 days before expiration
Certificate transparency monitoring to detect unauthorised issuance
Regular rotation of encryption keys following industry standards
Documented procedures for emergency certificate revocation
Backup certificates stored securely for disaster recovery
Automate vendor onboarding and risk scoring using AI-driven platforms that analyse vendor applications against security criteria. Machine learning models can assess business legitimacy, financial stability, and security posture based on submitted documentation and external data sources. This automation maintains consistent standards whilst processing applications at scale.

Integrate payment split solutions like Stripe Connect or PayPal Commerce Platform that handle complex multi-party transactions securely. These platforms manage PCI-DSS compliance for payment processing, automatically splitting revenue between your marketplace and vendors whilst handling tax calculations and fraud detection. Configure payout schedules that balance vendor cash flow needs with your risk management requirements.
Network segmentation creates security boundaries between different marketplace functions. Vendors access your platform through a dedicated network zone with strict firewall rules. Payment processing occurs in an isolated PCI-DSS compliant environment. Your core business logic and customer data reside in protected zones with no direct vendor access. This defence-in-depth approach contains breaches and limits damage.
Pro Tip: Implement API rate limiting and throttling to prevent abuse and denial-of-service attacks from compromised vendor accounts. Set reasonable limits based on legitimate business needs, then monitor for accounts exceeding thresholds. This protects your infrastructure whilst maintaining service quality for compliant vendors.
Microservices architecture with real-time inventory synchronisation prevents overselling, a critical issue in multi-vendor marketplaces. Use event-driven architecture where inventory changes trigger immediate updates across all systems. Implement optimistic locking for concurrent order processing, ensuring inventory decrements happen atomically. Webhooks notify vendors instantly when orders are placed, enabling rapid fulfilment.
Security control | Implementation approach | Business benefit |
|---|---|---|
OAuth 2.0 + RBAC | Token-based API access with granular permissions | 43% reduction in security incidents |
TLS 1.3 encryption | All data in transit and at rest encrypted | PCI-DSS compliance, customer trust |
AI-driven onboarding | Automated risk scoring and verification | Scale vendor acquisition efficiently |
Payment split automation | Stripe Connect or PayPal integration | Reduced operational overhead |
Microservices + webhooks | Event-driven real-time synchronisation | Eliminates overselling, improves experience |
Your ecommerce integration architecture should support diverse vendor systems without compromising security. Provide well-documented REST APIs with comprehensive authentication and authorisation examples. Offer SDKs in popular programming languages that handle security best practices automatically. Create sandbox environments where vendors can test integrations safely before going live.
Implement comprehensive logging that captures all vendor actions, API calls, and data access patterns. These audit trails prove invaluable for investigating security incidents, demonstrating compliance during audits, and identifying operational issues. Store logs in immutable storage with retention periods meeting regulatory requirements. Use log aggregation tools that enable rapid searching and analysis across distributed systems.
Verification, continuous compliance and vulnerability management
Secure marketplace operations require ongoing vigilance, not just initial setup. Establish continuous monitoring systems that track vendor risk scores, detect anomalous behaviour, and alert security teams to potential breaches. Modern security information and event management platforms correlate data from multiple sources to identify sophisticated attacks that individual systems might miss.
Vendor risk scoring should update dynamically based on multiple factors. Monitor for security incidents reported in vendor domains, changes in business stability indicators, customer complaint patterns, and compliance with marketplace policies. Automated systems can flag high-risk vendors for additional scrutiny whilst maintaining efficient operations for compliant partners.
GDPR compliance demands continuous attention to data processing activities, consent management, and individual rights requests. Implement automated workflows that handle data subject access requests by collecting information from all vendor systems touching that customer. Create processes for right-to-erasure requests that ensure complete deletion across distributed systems. Document your legal basis for processing and maintain records demonstrating compliance.
Automated security scanning identifies vulnerabilities before attackers exploit them. Tools like Snyk analyse application dependencies for known security flaws, whilst AWS Inspector examines infrastructure configurations against best practices. Leading marketplaces remediated 2,400+ vulnerabilities across 100+ applications using automated vulnerability management programs.
Establish tiered compliance verification processes that allocate resources based on risk. High-risk vendors require quarterly security audits, whilst lower-risk vendors undergo biannual reviews. This risk-based approach maintains security standards without overwhelming your compliance team. Document verification procedures and maintain evidence of completed audits for regulatory examination.
Pro Tip: Create a vendor security scorecard visible in their dashboard showing compliance status, outstanding security requirements, and improvement recommendations. This transparency motivates vendors to maintain security standards whilst reducing support requests about compliance expectations.
Compare manual versus automated vulnerability management approaches:
Approach | Detection speed | Coverage | Error rate | Scalability | Cost efficiency |
|---|---|---|---|---|---|
Manual scanning | Days to weeks | Limited by team capacity | 15-20% false negatives | Poor | Low |
Automated scanning | Minutes to hours | Comprehensive across all assets | 5-8% false positives | Excellent | High |
Hybrid approach | Hours to days | Comprehensive with context | 3-5% combined errors | Good | Moderate |
Integrate compliance dashboards accessible to security teams and executive stakeholders. Security operations centres need real-time visibility into active threats, vulnerability remediation status, and incident response activities. Executives require high-level metrics showing overall security posture, compliance status, and risk trends. Board presentations should include security KPIs alongside financial and operational metrics.
Incident response procedures must account for multi-vendor complexity. When a security incident occurs, you need processes to quickly identify affected vendors, contain the breach, notify impacted parties, and coordinate remediation. Conduct tabletop exercises simulating various incident scenarios to validate your response procedures and identify gaps before real incidents occur.
Regular penetration testing by qualified third parties identifies vulnerabilities that automated tools miss. Schedule annual comprehensive assessments covering your entire marketplace infrastructure, vendor portals, and API endpoints. Address identified vulnerabilities promptly, prioritising based on exploitability and potential impact. Maintain a vulnerability disclosure program allowing security researchers to report issues responsibly.
Your security verification processes should include:
Continuous automated vulnerability scanning with weekly reports
Quarterly vendor security audits for high-risk partners
Biannual compliance assessments against PCI-DSS and GDPR
Annual penetration testing by certified ethical hackers
Real-time monitoring of security events and anomalies
Monthly security awareness training for all marketplace staff
Maintain detailed documentation of all security controls, compliance procedures, and audit results. This documentation serves multiple purposes: training new team members, demonstrating compliance to auditors and partners, and providing evidence during incident investigations. Use a centralised knowledge management system that keeps documentation current as your security posture evolves.
Secure your enterprise multi-vendor marketplace with Ultra Commerce
Building a secure multi-vendor marketplace requires sophisticated technology and deep expertise in enterprise ecommerce security. Ultra Commerce provides a comprehensive platform specifically designed for enterprise organisations launching complex marketplace operations with security and compliance built into every component.
Our multi-vendor marketplace platform includes native vendor management, automated security controls, and compliance frameworks that accelerate your time to market whilst maintaining enterprise-grade security. The composable architecture integrates seamlessly with your existing systems, eliminating the need for costly replatforming whilst adding advanced capabilities.
Ultra Commerce supports complex B2C, B2B, and C2C transactions through intelligent routing, automated settlement, and comprehensive governance tools. Our enterprise ecommerce platform scales globally whilst maintaining the security and reliability that large organisations demand. Recognised in Gartner’s Magic Quadrant, we deliver the proven capabilities needed for mission-critical marketplace operations.
Explore how the Ultra Commerce platform can accelerate your secure marketplace implementation with modular components including PIM, OMS, and AI-driven orchestration that work together seamlessly or integrate with your existing technology investments.
Frequently asked questions about secure marketplace setup
What are the main benefits of implementing RBAC in multi-vendor marketplaces?
Role-based access control reduces security incidents by 43% by ensuring vendors can only access their own data and authorised platform features. RBAC simplifies permission management at scale, enables rapid vendor onboarding with predefined roles, and provides clear audit trails showing exactly what each vendor accessed.
How do I ensure PCI-DSS compliance in a multi-vendor marketplace?
Implement network segmentation isolating payment processing from other systems, use PCI-DSS compliant payment gateways like Stripe Connect, encrypt all cardholder data with TLS 1.3, and conduct quarterly vulnerability scans. Maintain detailed documentation of your cardholder data environment and complete annual compliance assessments by qualified security assessors.
Why is automated vendor onboarding more secure than manual processes?
Automated onboarding with AI-driven risk scoring applies consistent security criteria to every vendor application, eliminating human error and bias. Machine learning models detect fraudulent applications by analysing patterns across multiple data sources, whilst automation ensures all required security documentation is collected and verified before granting platform access.
How does continuous monitoring support GDPR compliance?
Continuous monitoring tracks data processing activities across all vendor systems, ensuring you can demonstrate compliance with GDPR’s accountability principle. Automated alerts notify you immediately when vendors access customer data inappropriately or when data subject rights requests require action. Real-time monitoring also detects potential data breaches within the 72-hour notification window GDPR requires.
What’s the difference between automated and manual vulnerability management?
Automated vulnerability management scans your entire infrastructure continuously, detecting new vulnerabilities within hours and eliminating the 15-20% false negative rate of manual approaches. Whilst automation generates some false positives, it scales effortlessly across hundreds of applications and provides consistent coverage that manual processes cannot match at enterprise scale.









